[КИОШ] ЦаНКПіЕх ЙЋРлРЇ ДыРд АјАн ЙцОюИІ РЇЧб "fail2ban МГФЁ Йз МГСЄ"
МЙіПюПЕРЛ ЧЯДйКИИщ SSH,FTPЕюРЛ ХыЧи ПмКЮПЁМ ОЫ Мі ОјДТ IPАЁ АшСЄСЂБй НУЕЕЧЯДТ АцПьАЁ РжНРДЯДй.
БзФЁИИ ЦаНКПіЕхИІ И№ИЃДЯ, СЂБйНЧЦаАЁ ЕЩ АЭРдДЯДй..
БзЗБЕЅ РЬЕщРК ЧиХЗЧСЗЮБзЗЅРЛ РЬПыЧЯПЉ СЂМгРЬ ЕЩЖЇБюСі ЦаНКПіЕхИІ АшМг ЙйВйИч, АшМг СЂБйРЛ НУЕЕЧв АЬДЯДй..
АсБЙ ЦаНКПіЕхАЁ ЖеИЎИч root АшСЄПЁ СЂМгЕЩ АЭРдДЯДй.
РЬ ЙЎСІИІ ЧиАсЧЯБтРЇЧиМДТ АЃДмЧЯАд АќИЎРк IPИИ МЙіСЂБйРЛ ЧуПыЧЯИщ ЕЫДЯДй.
ЧЯСіИИ, АќИЎРкIPАЁ РЏЕПРЬАХГЊ ДйИЅ ПмКЮПЁМ СЂБйЧв АцПьЕЕ РжРЛ Мі РжНРДЯДй.
БзЗГ ТїМБУЅРИЗЮ ИюШИ РЬЛѓ СЂБйПЁ НЧЦаЧв АцПь ЧиДч СЂБйIPИІ ПЯРќШїЖЧДТ РЯСЄНУАЃ ЕПОШРК ТїДм ЧиОп РЬЗБ АјАнПЁ ДыКёЧв Мі РжАкСіПф..
ПЉБтМДТ fail2ban РЬЖѕ ЧСЗЮБзЗЅРЛ РЬПыЧи ЙЋРлРЇ АјАнЙцОюИІ ЧиКМБюЧеДЯДй.
fail2banЧСЗЮБзЗЅРК СЂБйЗЮБзЦФРЯПЁМ НЧЦаШНМіИІ АшЛъЧЯАэ iptablesРЛ РЬПыЧи МЙіСЂБйРЛ ТїДмЧЯДТ ХјРдДЯДй.
ОЦТќ, ОЦЗЁРЧ МГФЁАњСЄАњ МГСЄРК centos6ПЁМ СјЧр ЧпРИДЯ, ДйИЅ ИЎДЊНКПЁМДТ ДйИІ Мі РжНРДЯДй.
fail2ban МГФЁ
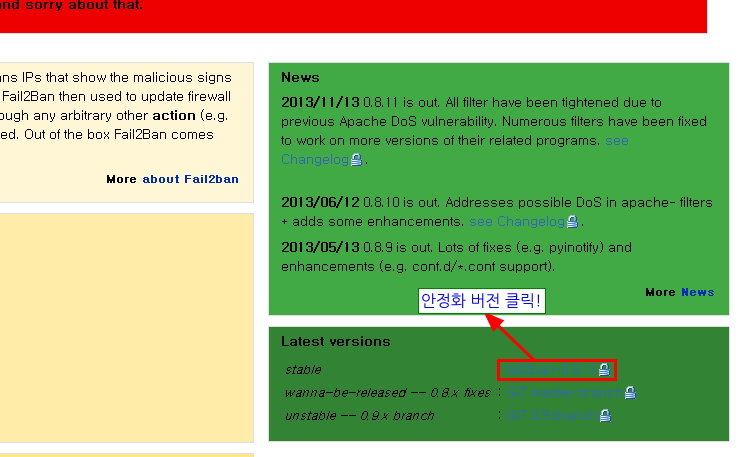
1. ИеРњ http://www.fail2ban.org ПЁМ fail2ban ДйПюЗЮЕх ЧеДЯДй.
# tar zxvf fail2ban-0.8.11.tar.gz# cd fail2ban-0.8.11# python setup.py install
# cp files/redhat-initd /etc/init.d/fail2ban
# chkconfig --add fail2ban# chkconfig fail2ban on
*МГСЄЦФРЯПЁМ МГСЄ (ПЉБтПЁМБ vi ЦэС§БтИІ РЬПыЧи КЏАцЧЯАкНРДЯДй.)
# vi /etc/fail2ban/jail.conf
-> 29СйТыПЁМКЮХЭ ~ (РЬКЮКаРК ПјЧЯНУДТ АЊРИЗЮ МГСЄЧЯММПф.)
# "ignoreip" can be an IP address, a CIDR mask or a DNS host. Fail2ban will not
# ban a host which matches an address in this list. Several addresses can be
# defined using space separator.
ignoreip = 127.0.0.1/8 #РдЗТЧЯНХ IPЗЮ СЂБйНУ ОЦЙЋИЎ НЧЦаЧиЕЕ ТїДмЕЧСіОЪНРДЯДй. (АќИЎРкIPИІ РћОюЕЮНУИщ ЕЧАкГзПф)
# "bantime" is the number of seconds that a host is banned.
bantime = 600 #РЯСЄШНМі УЪАњНУЕЕНУ СЂБйАХКЮ НУАЃРдДЯДй. (ДмРЇ : УЪ)
# A host is banned if it has generated "maxretry" during the last "findtime"
# seconds.
findtime = 600 #РдЗТЧЯНХ НУАЃАЃАн ЛчРЬПЁ СіСЄШНМіИІ УЪАњНУ ТїДмЧеДЯДй. (ДмРЇ : УЪ)
# "maxretry" is the number of failures before a host get banned.
maxretry = 3 #РдЗТЧЯНХ ШНМіУЪАњНУ СЂБйАХКЮЧеДЯДй.
-> 72СйТы КЮХЭ ~
[ssh-iptables]
enabled = true #РЬКЮКаРЛ trueЗЮ ЧиСрОп sshСЂБйНУ fail2banАЁ ЕПРлЕЩ Мі РжНРДЯДй.
filter = sshd
action = iptables[name=SSH, port=ssh, protocol=tcp]
sendmail-whois[name=SSH, dest=you@example.com, sender=fail2ban@example.com, sendername="Fail2Ban"]
logpath = /var/log/secure #ssh СЂБйЗЮБзЦФРЯРЛ РдЗТЧиСжММПф. ЗЮБзЦФРЯРК ИЎДЊНКИЖДй ДйИЈДЯДй. centos6.4АцПь "/var/log/secure" РдДЯДй. ЗЮБзЦФРЯРЬ СИРчЧЯСіОЪРИИщ МКёНКНЧЧр НЧЦаЕЫДЯДй.
maxretry = 5 #РдЗТЧЯНХ ШНМіУЪАњНУ СЂБйАХКЮЧеДЯДй. (РМГСЄАњ ЛѓАќОјРЬ sshСЂБйПЁИИ РћПыЕЫДЯДй. ЛшСІЧЯНУИщ РМГСЄРЬ РћПыЕЫДЯДй.)
- УпШФ МГСЄЦФРЯРЛ КЏАцЧЯИщ ЙнЕхНУ МКёНКРчНУРл(# service fail2ban restart)РЛ ЧиСрОп РћПыЕЫДЯДй.
*МКёНК НУРл
# service fail2ban start
- МКёНК НЧЧрНУ [OK]АЁ ГЊПЭОп СЄЛѓЕПРлРдДЯДй.
ЁиНЧЦаТїДмНУ iptablesПЁМ IPИІ ТїДмЧЯАэ РжОюМ iptablesПЁМ ТїДмЕШ IPШЎРЮЙз ТїДмЧиСІИІ Чв Мі РжНРДЯДй.
* fail2banПЁМ ТїДмЕШ ip ЧиСІ
- iptables -D fail2ban-ProFTPD -s xxx.xxx.xxx.xxx -j REJECT
- iptables -D fail2ban-SSH -s xxx.xxx.xxx.xxx -j REJECT